The Standard attribute (92), when used in an ACL without the HP-Nas-Rules-IPv6 VSA, filters IPv4 traffic inbound from the authenticated client. (Any IPv6 traffic inbound from the client is dropped.) This example illustrates configuring RADIUS-assigned IPv4 ACL support on FreeRADIUS using the standard attribute for two different client identification methods (username/password and MAC address).
-
Enter the ACL standard attribute in the FreeRADIUS
dictionary.rfc4849file.ATTRIBUTE Nas-FILTER-Rule 92
-
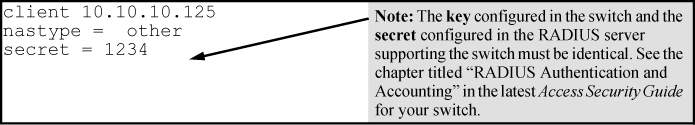
Enter the switch IP address, NAS (Network Attached Server) type, and the key used in the FreeRADIUS clients.conf file. For example, if the switch IP address is 10.10.10.125 and the key ("secret") is "1234", you would enter the following in the server's clients.conf file:
-
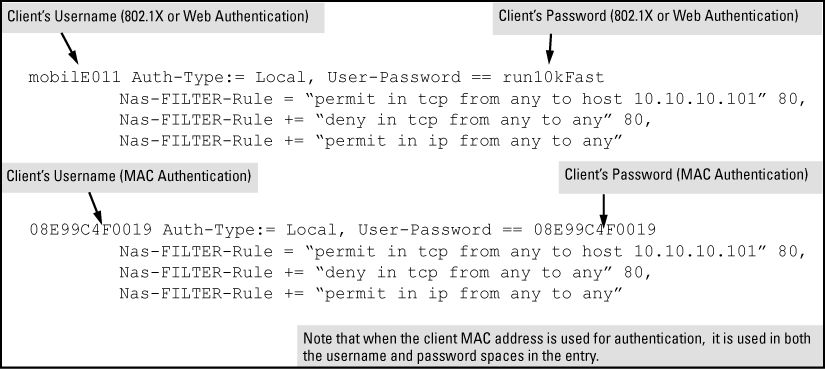
For a given client username/password pair or MAC address, create an ACL by entering one or more ACEs in the FreeRADIUS "users" file. Remember that every ACL created automatically includes an implicit deny in ip from any to any ACE.
For example, to create identical ACL support for the following:
-
Client having a username of "mobilE011" and a password of "run10kFast"
-
Client having a MAC address of 08 E9 9C 4F 00 19
The ACL in this example must achieve the following:
-
Permit http (TCP port 80) traffic from the client to the device at 10.10.10.101
-
Deny http (TCP port 80) traffic from the client to all other devices
-
Permit all other traffic from the client to all other devices
![[NOTE: ]](images/note.gif)
NOTE: For information on syntax details for RADIUS-assigned ACLs, see Using HP VSA 63 to assign IPv6 and IPv4 ACLs.
To configure the above ACL, enter the username/password and ACE information shown in Configuring the FreeRADIUS server to support ACLs for the indicated clients.
-
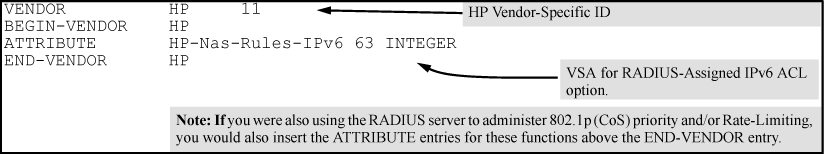
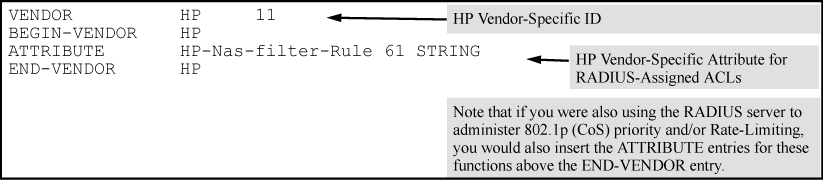
The ACL VSA HP-Nas-Rules-IPv6=1 is used in conjunction with the standard attribute (Nas-Filter-Rule) for ACL assignments filtering both IPv6 and IPv4 traffic inbound from an authenticated client. For example, to use these attributes to configure a RADIUS-assigned ACL on a FreeRADIUS server to filter both IPv6 and IPv4 ACLs, perform these steps:
-
Enter the following in the FreeRADIUS
dictionary.hpfile:-
HP vendor-specific ID
-
ACL VSA for IPv6 ACLs (63)
-
HP-Nas-Rules-IPv6 VALUE setting to specify both IPv4 and IPv6 (1)
-
-
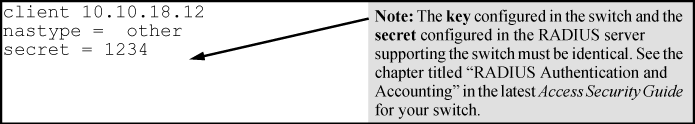
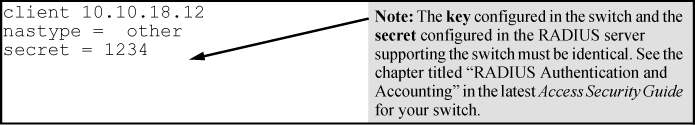
Enter the switch IPv4 address, NAS (Network Attached Server) type, and the key used in the FreeRADIUS clients.conf file. For example, if the switch IP address is 10.10.10.125 and the key ("secret") is "1234", you would enter the following in the server's clients.conf file:
-
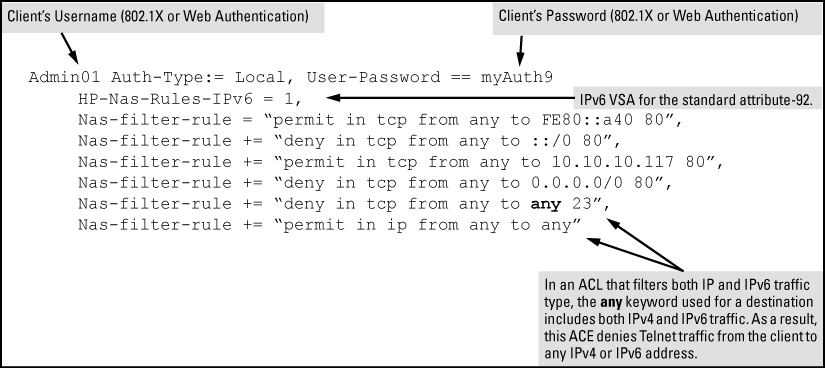
For a given client username/password pair, create an ACL by entering one or more IPv6 and IPv4 ACEs in the FreeRADIUS "users" file. Remember that the ACL created to filter both IPv4 and IPv6 traffic automatically includes an implicit deny in ip from any to any ACE at the end of the ACL in order to drop any IPv4 and IPv6 traffic that is not explicitly permitted or denied by the ACL. For example, to create ACL support for a client having a username of "Admin01" and a password of "myAuth9". The ACL in this example must achieve the following:
-
Permit http (TCP port 80) traffic from the client to the device at FE80::a40.
-
Deny http (TCP port 80) traffic from the client to all other IPv6 addresses.
-
Permit http (TCP port 80) traffic from the client to the device at 10.10.10.117.
-
Deny http (TCP port 80) traffic from the client to all other IPv4 addresses.
-
Deny Telnet (TCP port 23) traffic from the client to any IPv4 or IPv6 addresses.
-
Permit all other IPv4 and IPv6 traffic from the client to all other devices.
To configure the above ACL, enter the username/password and ACE information, as shown in this example:
-
This continues to support the HP VSA 61 vendor-specific method of earlier releases for enabling RADIUS-based IPv4 ACL assignments on the switch. The recommended use of this option is to support legacy ACL configurations that rely on VSA 61. HP recommends using the standard attribute (92) for new, RADIUS-based IPv4 ACLs, see Nas-Filter-Rule-Options, and ACE syntax configuration options in a RADIUS server, using the standard attribute in an IPv4 ACL (Example).
This example uses the HP VSA attribute 61 for configuring RADIUS-assigned IPv4 ACL support on FreeRADIUS for two different client identification methods (username/password and MAC address).
-
Enter the HP vendor-specific ID and the ACL VSA in the FreeRADIUS dictionary file:
-
Enter the switch IPv4 address, NAS (Network Attached Server) type, and the key used in the FreeRADIUS
clients.conffile. For example, if the switch IP address is 10.10.10.125 and the key ("secret") is "1234", you would enter the following in the server'sclients.conffile: -
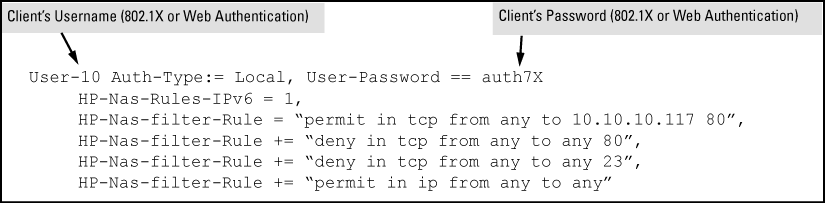
For a given client username/password pair, create an ACL by entering one or more IPv4 ACEs in the FreeRADIUS "users" file. Remember that the ACL created to filter IPv4 traffic automatically includes an implicit
deny in ip from anyto any ACE (for IPv4). For example, to create ACL support for a client having a username of "User-10" and a password of "auth7X". The ACL in this example must achieve the following:-
Permit http (TCP port 80) traffic from the client to the device at 10.10.10.117.
-
Deny http (TCP port 80) traffic from the client to all other IPv4 addresses.
-
Deny Telnet (TCP port 23) traffic from the client to any IPv4 address.
-
Permit all other IPv4 traffic from the client to all other devices.
To configure the above ACL, you would enter the username/password and ACE information shown in Configuring a FreeRADIUS server to filter IPv4 traffic for a client with the correct credentials into the FreeRADIUS "users"file.
-
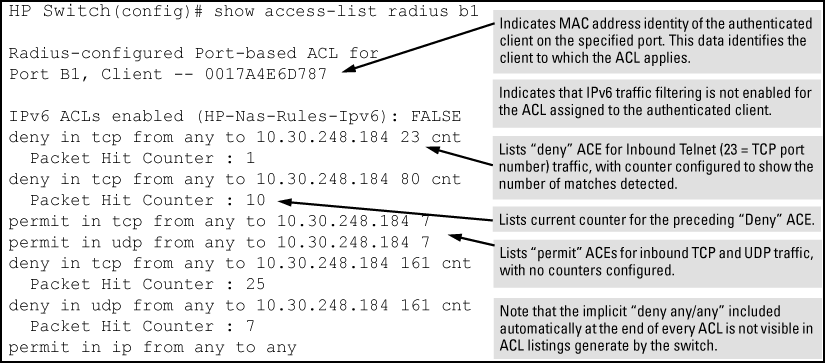
These commands output data indicating the current ACL activity imposed per-port by RADIUS server responses to client authentication.
Syntax:
For the specified ports, this command lists:
Whether the ACL for the indicated client is configured to filter IPv4 traffic only, or both IPv4 and IPv6 traffic. See Nas-Filter-Rule attribute options for more on this topic.
The explicit ACEs, switch port, and client MAC address for each ACL dynamically assigned by a RADIUS server as a response to client authentication.
If
cnt(counter) is included in an ACE, then the output includes the current number of inbound packet matches the switch has detected in the current session for that ACE, see ACE syntax in RADIUS servers.Note: If there are no ACLs currently assigned to any port in
<port-list>, executing this command returns only the system prompt. If a client authenticates but the server does not return a RADIUS-assigned ACL to the client port, then the server does not have a valid ACL configured and assigned to that client's authentication credentials.
Example:
The following output shows that a RADIUS server has assigned an ACL to port B1 to filter inbound traffic from an authenticated client identified by a MAC address of 00-17-A4-E6-D7-87.
Syntax:
For ports in < configured for authentication, this command shows the details of the RADIUS-assigned features listed below that are active as the result of a client authentication. (Ports in port-list>< that are not configured for authentication are not listed.)port-list>
-
Client Base Details:
Indicates whether there is an authenticated client session active on the port. Options include
authenticatedandunauthenticated.During an authenticated session, shows the user name of the authenticated client. If the client is not authenticated, this field is empty.
Shows the authenticated client's IP address, if available. Requires DHCP snooping enabled on the switch. When "n/a" appears in the field, the switch has not been able to acquire the client's IP address. Note: Where the client IP address is available to the switch, it can take a minute or longer for the switch to learn the address. For more on this topic, see Configuring RADIUS accounting.
For an unauthenticated session, indicates the elapsed time in seconds since the client was detected on the port. For an authenticated session, this indicates the elapsed time in seconds since the client was authenticated on the port.
During an authenticated session, shows the MAC address of the authenticated client.
-
Access Policy Details:
Indicates the 802.1p priority assigned by the RADIUS server for traffic inbound on the port from an authenticated client. The field shows an eight-digit value where all digits show the same, assigned 802.1p number. For example, if the assigned 802.1p value is 5, then this field shows
55555555. If an 802.1p priority has not been assigned by the RADIUS server, this field showsNot Defined.VLAN ID (VID) of the untagged VLAN currently supporting the authenticated connection.
VLAN IDs (VIDs) of any tagged VLANs currently supporting the authenticated connection.
Lists the explicit ACEs in the ACL assigned to the port for the authenticated client. Includes the ACE "Hit Count" (matches) for ACEs configured with the
cntoption, see ACE syntax in RADIUS servers. If a RADIUS ACL for the authenticated client is not assigned to the port,No Radius ACL Listappears in this field.Indicates the ingress rate-limit assigned by the RADIUS server to the port for traffic inbound from the authenticated client. If there is no ingress rate-limit assigned, then
Not Setappears in this field.Indicates the egress rate-limit assigned by the RADIUS server to the port for traffic outbound to the authenticated client. If there is no egress rate-limit assigned, then
Not Setappears in this field.
Output showing current RADIUS-applied features
HP Switch(config)# show port-access web-based clients 10 detailed
Port Access Web-Based Client Status Detailed
Client Base Details :
Port : 9
Session Status : authenticated Session Time(sec) : 5
Username : acluser1 MAC Address : 0017a4-e6d787
IP : n/a
Access Policy Details :
COS Map : 77777777 In Limit Kbps : 1000
Untagged VLAN : 10 Out Limit Kbps : Not Set
Tagged VLANs : 20
RADIUS-ACL List :
deny in 23 from any to 10.0.8.1/24 23 CNT
Hit Count: 1
permit in 1 from any to 10.0.10.1/24 CNT
Hit Count: 112
deny in udp from any to any 67-68 CNT
Hit Count: 7
permit in ip from any to any CNT
Hit Count: 125
ICMP type numbers and keywords
| IPv4 ICMP | IPv6 ICMP | ||
|---|---|---|---|
| # | Keyword | # | Keyword |
| 0 | echo reply | 1 | destination unreachable |
| 3 | destination unreachable | 2 | packet too big |
| 4 | source quench | 3 | time exceeded |
| 5 | redirect | 4 | parameter problem |
| 8 | echo request | 128 | echo request |
| 9 | router advertisement | 129 | echo reply |
| 10 | router solicitation | 130 | multicast listener query |
| 11 | time-to-live exceeded | 131 | multicast listener reply |
| 12 | IP header bad | 132 | multicast listener done |
| 13 | timestamp request | 133 | router solicitation |
| 14 | timestamp reply | 134 | router advertisement |
| 15 | information request | 135 | neighbor solicitation |
| 16 | information reply | 136 | neighbor advertisement |
| 17 | address mask request | 137 | redirect message |
| 18 | address mask reply | 138 | router renumbering |
| 139 | icmp node information query | ||
| 140 | icmp node information response | ||
| 141 | inverse neighbor discovery solicitation message | ||
| 142 | inverse neighbor discovery advertisement message | ||
| 143 | version 2 multicast listener report | ||
| 144 | home agent address discovery request message | ||
| 145 | home agent address discovery reply message | ||
| 146 | mobile prefix solicitation | ||
| 147 | mobile prefix advertisement | ||
| 148 | certification path solicitation message | ||
| 149 | certification path advertisement message | ||
| 151 | multicast router advertisement | ||
| 152 | multicast router solicitation | ||
| 153 | multicast router termination | ||