Configure RADIUS authentication for controlling access through one or more of the following:
-
Serial port
-
Telnet
-
SSH
-
Port-Access (802.1X)
-
WebAgent
-
RADIUS authentication on the switch must be enabled to override the default authentication operation which is to automatically assign an authenticated client to the operator privilege level. This applies the privilege level specified by the service type value received from the RADIUS server, see Configuring authentication for the access methods that RADIUS protects.
-
Configure the switch for accessing one or more RADIUS servers (one primary server and up to two backup servers):
-
Server IP address
-
(Optional) UDP destination port for authentication requests (default: 1812; recommended)
-
(Optional) UDP destination port for accounting requests (default: 1813; recommended)
-
(Optional) Encryption key for use during authentication sessions with a RADIUS server. This key overrides the global encryption key you can also configure on the switch, and must match the encryption key used on the specified RADIUS server. (default: null)
![[NOTE: ]](images/note.gif)
NOTE: Step 2 assumes you have already configured the RADIUS servers to support the switch. See your RADIUS server documentation for details.
-
-
Configure the global RADIUS parameters.
-
Server key: This key must match the encryption key used on the RADIUS servers the switch contacts for authentication and accounting services unless you configure one or more per-server keys.(default: null)
-
Timeout period: The timeout period the switch waits for a RADIUS server to reply. (default: 5 seconds; range: 1 to 15 seconds)
-
Retransmit attempts: The number of retries when there is no server response to a RADIUS authentication request. (default: 3; range of 1 to 5)
-
Server dead-time: The period during which the switch will not send new authentication requests to a RADIUS server that has failed to respond to a previous request. This avoids a wait for a request to time out on a server that is unavailable. If you want to use this feature, select a dead-time period of 1 to 1440 minutes. (default: disabled; range: 1-1440 minutes.) If your first-choice server was initially unavailable, but then becomes available before the dead-time expires, you can nullify the dead-time by resetting it to zero and then trying to log on again. As an alternative, you can reboot the switch, (thus resetting the dead-time counter to assume the server is available) and then try to log on again.
-
Number of login attempts: This is actually an
aaa authenticationcommand. It controls how many times per session a RADIUS client (and clients using other forms of access) can try to log in with the correct username and password. (default: Three times per session)
-
For RADIUS accounting features, see Accounting services.
Configure the switch for RADIUS authentication through the following access methods:
You can configure RADIUS as the primary password authentication method for the above access methods. You also need to select either local, none, or authorized as a secondary, or backup, method. Note that for console access, if you configure radius (or tacacs) for primary authentication, you must configure local for the secondary method. This prevents the possibility of being completely locked out of the switch in the event that all primary access methods fail.
Syntax:
aaa authentication <console|telnet|ssh|web|<enable|login <local|radius>> web-based|mac-based <chap-radius|peap-radius>>Configures RADIUS as the primary password authentication method for console, Telnet, SSH, and/or the WebAgent.
In certain situations, RADIUS servers can become isolated from the network. Users are not able to access the network resources configured with RADIUS access protection and are rejected. To address this situation, configuring the authorized secondary authentication method allows users unconditional access to the network when the primary authentication method fails because the RADIUS servers are unreachable.
|
|
|
![[CAUTION: ]](images/caution.gif) |
CAUTION: Configuring |
|
|
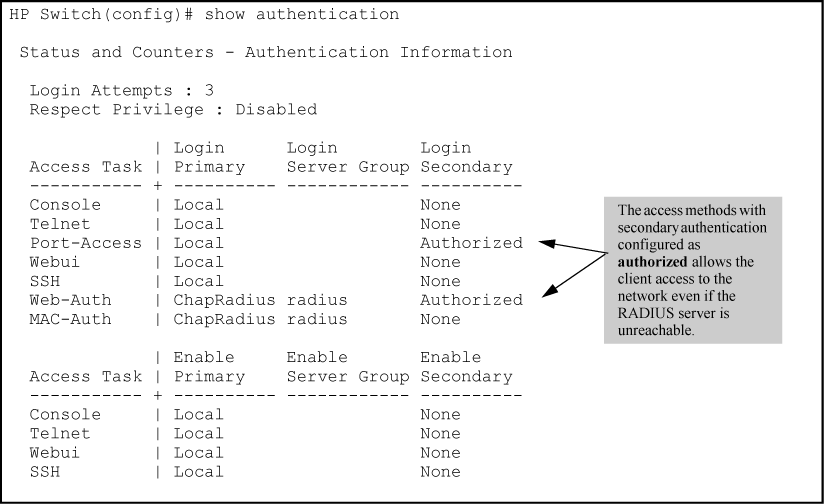
Example of AAA authentication using authorized for the secondary authentication method shows an example of the show authentication command displaying authorized as the secondary authentication method for port-access, web-based authentication access, and MAC authentication access. Since the configuration of authorized means no authentication will be performed and the client has unconditional access to the network, the "Enable Primary" and "Enable Secondary" fields are not applicable (N/A).
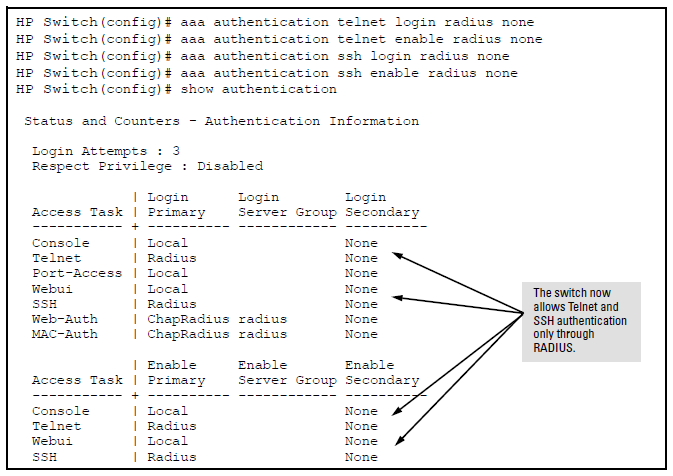
Suppose you already configured local passwords on the switch, but want RADIUS to protect primary Telnet and SSH access without allowing a secondary Telnet or SSH access option (the switch local passwords):
|
|
|
![[NOTE: ]](images/note.gif) |
NOTE: If you configure the Login Primary method as |
|
|
In the default RADIUS operation, the switch automatically admits any authenticated client to the login (operator) privilege level, even if the RADIUS server specifies enable (manager) access for that client. Thus, an authenticated user authorized for the manager privilege level must authenticate again to change privilege levels. Using the optional login privilege-mode command overrides this default behavior for clients with enable access. That is, with privilege-mode enabled, the switch immediately allows enable (manager) access to a client for whom the RADIUS server specifies this access level.
Syntax:
When enabled, the switch reads the Service-Type field in the client authentication received from a RADIUS server. The following table describes the applicableService-Type values and corresponding client access levels the switch allows upon authentication by the server.
This feature applies to console (serial port), Telnet, SSH, and WebAgent access to the switch. It does not apply to 802.1X port-access.
The
noform of the command returns the switch to the default RADIUS authentication operation. The default behavior for most interfaces is that a client authorized by the RADIUS server for Enable (manager) access will be prompted twice, once for Login (operator) access and once for Enable access. In the default RADIUS authentication operation, the WebAgent requires only one successful authentication request. For more information on configuring the Service Type in your RADIUS application, see the documentation provided with the application.
This section describes how to configure the switch to interact with a RADIUS server for both authentication and accounting services.
|
|
|
![[NOTE: ]](images/note.gif) |
NOTE: If you want to configure RADIUS accounting on the switch, see Accounting services. |
|
|
Syntax:
Adds a server to the RADIUS configuration or (with
no) deletes a server from the configuration. You can configure up to three RADIUS servers, and up to 15 RADIUS server addresses. See Using multiple RADIUS server groups for information about grouping multiple RADIUS servers.The switch uses the first server it successfully accesses, see Changing RADIUS-server access order.
The
oobmoption specifies that the RADIUS traffic will go through the out-of-band management (OOBM) port.Optional. Changes the UDP destination port for authentication requests to the specified RADIUS server (host). If you do not use this option with the
radius-server hostcommand, the switch automatically assigns the default authentication port number. Theauth-portnumber must match its server counterpart.
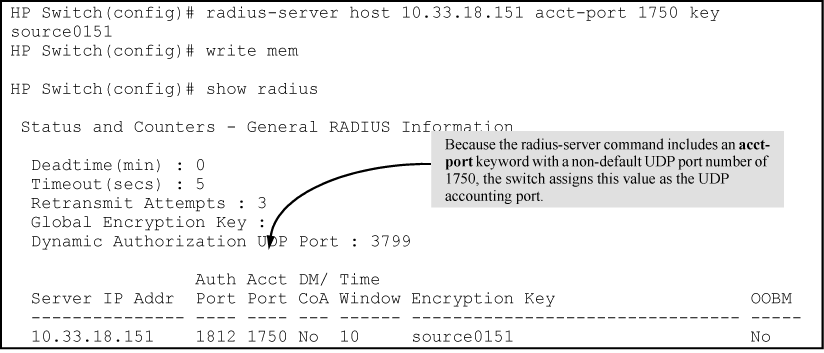
Optional. Changes the UDP destination port for accounting requests to the specified RADIUS server. If you do not use this option with the
radius-server hostcommand, the switch automatically assigns the default accounting port number. Theacct-portnumber must match its server counterpart.Enables or disables the processing of Disconnect and Change of Authorization messages from this host. When enabled, the RADIUS server can dynamically terminate or change the authorization parameters (such as VLAN assignment) used in an active client session on the switch. The UDP port specified in the
radius-server dyn-autz-portcommand (defaults to 3799) is the port used to listen for Change of Authorization messages (CoA) or Disconnect messages (DM). See Change-of-Authorization.Optional. Specifies an encryption key for use during authentication (or accounting) sessions with the specified server. This key must match the encryption key used on the RADIUS server. Use this command only if the specified server requires a different encryption key than configured for the global encryption key.
NOTE: Formerly, when you saved the configuration file using Xmodem or TFTP, the RADIUS encryption key information was not saved in the file. This caused RADIUS authentication to break when the startup configuration file was loaded back onto the switch. You now can save the configured RADIUS shared secret (encryption) key to a configuration file by entering the following commands:
The time window in seconds within which the received dynamic authorization requests are considered to be current and accepted for processing. A zero value means there is no time limit. A non-zero value indicates that the even-timestamp attribute is expected as part of all Change of Authorization and Disconnect request messages. If the timestamp attribute is not present the message is dropped.
Suppose you have configured the switch as shown in Configuration for RADIUS server before changing the key and adding another server and you now need to make the following changes:
Configuration for RADIUS server before changing the key and adding another server
HP Switch(config)# radius-server host 10.22.18.127 key source0127
HP Switch(config)# radius-server host 10.22.18.119 key source0119
HP Switch# show radius
Status and Counters - General RADIUS Information
Deadtime(min) : 0
Timeout(secs) : 5
Retransmit Attempts : 3
Global Encryption Key :
Dynamic Authorization UDP Port : 3799
Source IP Selection : Outgoing Interface
Auth Acct DM/ Time
Server IP Addr Port Port CoA Window Encryption Key OOBM
--------------- ---- ---- --- ------ ---------------------------
10.33.18.127 1812 1813 No 300 TempKey01 No
To make these changes, perform the following:
Configuration for RADIUS server after changing the key and adding another server
HP Switch(config)# radius-server host 10.33.18.127 key source0127 * HP Switch(config)# radius-server host 10.33.18.119 key source0119 ** HP Switch(config)# show radius Status and Counters - General RADIUS Information Deadtime(min) : 0 Timeout(secs) : 5 Retransmit Attempts : 3 Global Encryption Key :myg10balkey Dynamic Authorization UDP Port : 3799 Auth Acct DM/ Time Server IP Addr Port Port CoA Window Encryption Key --------------- ---- ---- --- ------ ---------------- 10.33.18.127 1812 1813 No 10 source0127 10.33.18.119 1812 1813 No 10 source0119
* Changes the key for the existing server to “source012 7” (step 1, above).
** Adds the new RADIUS server with its required “source0119” key.
To change the order in which the switch accesses RADIUS servers, see Changing RADIUS-server access order.
Configure the switch for the following global RADIUS parameters:
-
Number of login attempts: In a given session, this specifies how many tries at entering the correct username and password pair are allowed before access is denied and the session terminated. This is a general
aaa authenticationparameter and is not specific to RADIUS. -
Global server key: The server key the switch uses for contacts with all RADIUS servers for which there is not a server-specific key configured by
radius-server host <. This key is optional if you configure a server-specific key for each RADIUS server entered in the switch.ip-address> key <key-string> -
Server timeout: Defines the time period in seconds for authentication attempts. If the timeout period expires before a response is received, the attempt fails.
-
Server dead time: Specifies the time in minutes during which the switch avoids requesting authentication from a server that has not responded to previous requests.
-
Retransmit attempts: If the first attempt to contact a RADIUS server fails, this specifies how many retries to allow the switch to attempt on that server.
-
Change of Authorization port: The
dyn-autz-portparameter specifies the UDP port number that listens for the Change of Authorization and Disconnect messages.The UDP port range is 1024-49151. The default port is 3799.
Syntax:
Example:
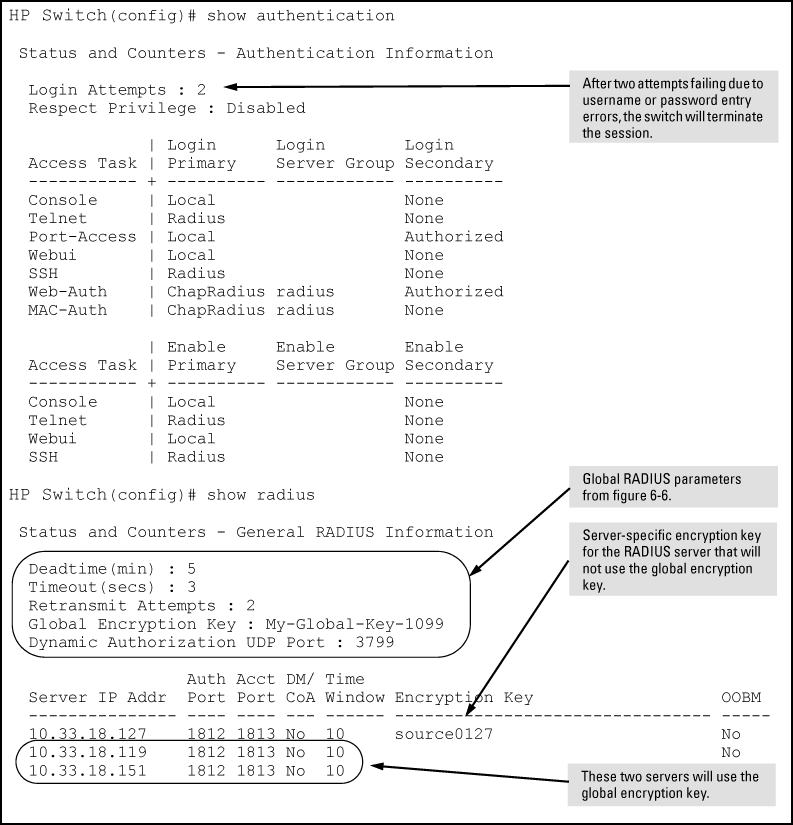
Suppose your switch is configured to use three RADIUS servers for authenticating access through Telnet and SSH. Two of these servers use the same encryption key. In this case the plan is to configure the switch with the following global authentication parameters:
-
Allow only two tries to correctly enter username and password.
-
Use the global encryption key to support the two servers that use the same key. (For this example, assume that you did not configure these two servers with a server-specific key.)
-
Use a dead-time of five minutes for a server that fails to respond to an authentication request.
-
Allow two retries following a request that did not receive a response.
Global configuration exercise for RADIUS authentication
HP Switch(config)# aaa authentication num-attempts 2 HP Switch(config)# radius-server key My-Global-KEY-1099 HP Switch(config)# radius-server dead-time 5 HP Switch(config)# radius-server timeout 3 HP Switch(config)# radius-server retransmit 2 HP Switch(config)# write mem
Listings of global RADIUS parameters configured in Global configuration exercise for RADIUS authentication
The authentication and accounting features on the switch can use up to fifteen RADIUS servers and these servers can be put into groups. Up to 5 groups of 3 RADIUS servers each can be configured. The authentication and accounting features can choose which RADIUS server group to communicate with. End-user authentication methods (802.1X, MAC-based and web-based) can authenticate with different RADIUS servers from the management interface authentication methods (console, telnet, ssh, web).
Several commands are used to support the RADIUS server group option. The RADIUS server must be configured before it can be added to a group. See Configuring the switch for RADIUS authentication for more information.
Syntax:
Syntax:
Associates a RADIUS server with a server group. Each group can contain up to 3 RADIUS servers. The default group (called ‘radius'), can only contain the first three RADIUS servers. The default group cannot be edited.
The
noform of the command removes the RADIUS server with the indicated IP address from the server group. If that server was the last entry in the group, the group is removed.
radius <: The group name of the RADIUS server group. The name has a maximum length of 12 characters. Up to five groups can be configured with a a maximum of three RADIUS servers in each group. The first group slot is used by the default group.group-name>
The following commands have the server-group option. If no server-group is specified, the default RADIUS group is used. The server group must already be configured.
|
|
|
![[NOTE: ]](images/note.gif) |
NOTE: The last RADIUS server in a server group cannot be deleted if any authentication or accounting method is using the server group. |
|
|
Syntax:
aaa authentication <console|telnet|ssh|web> <enable|[login <local]|radius [server-group <group-name>|local|none|authorized]Configures the primary password authentication method for console, Telnet, SSH, and the WebAgent.
<local|radius>
Use either the local switch user/password database or a RADIUS server for authentication.
Syntax:
aaa authentication <port-access <local|eap-radius|chap-radius>|<mac-based|web-based|<chap-radius|peap-mschapv2> [none|authorized|server-group|<group-name>]>>Configures the primary authentication method for port-access, MAC-based, or web-based access.
Password authentication for web-based or MAC-based port access to the switch. Use
peap-mschapv2for password verification without requiring access to a plain text password; it is more secure.Configures
local,chap-radius (MD5), oreap-radiusas the primary password authentication method for port-access.
Syntax:
Syntax:
Displays the same information as the
show radiuscommand, but displays the servers in their server groups.
Output from the show server-group radius command
HP Switch(config)# show server-group radius
Status and Counters - AAA Server Groups
Group Name: radius
Auth Acct DM/ Time
Server IP Addr Port Port CoA Window Encryption Key
--------------- ----- ----- ---- ------- --------------------
192.168.1.3 1812 1813 No 300 default_key
192.168.3.3 1812 1813 No 300 grp2_key
192.172.4.5 1812 1813 No 300 grp2_key
192.173.6.7 1812 1813 No 300 grp2_key
Group Name: group2
Auth Acct DM/ Time
Server IP Addr Port Port CoA Window Encryption Key
--------------- ----- ----- ---- ------- --------------------
192.168.3.3 1812 1813 No 300 grp2_key
192.172.4.5 1812 1813 No 300 grp2_key
192.173.6.7 1812 1813 No 300 grp2_key
Group Name: group3
Auth Acct DM/ Time
Server IP Addr Port Port CoA Window Encryption Key
--------------- ----- ----- ---- ------- --------------------
192.168.30.3 1812 1813 No 300 grp3_key
192.172.40.5 1812 1813 No 300 grp3_key
192.173.60.7 1812 1813 No 300 grp3_key
Output from the show authentication command
HP Switch(config)# show authentication
Status and Counters - Authentication Information
Login Attempts : 3
Respect Privilege : Disabled
| Login Login Login
Access Task | Primary Server Group Secondary
----------- + ---------- ------------ ----------
Console | Local radius None
Telnet | Local radius None
Port-Access | Local None
Webui | Local None
SSH | Local None
Web-Auth | ChapRadius group3 None
MAC-Auth | ChapRadius group3 None
| Enable Enable Enable
Access Task | Primary Server Group Secondary
----------- + ---------- ------------ ----------
Console | Local radius None
Telnet | Radius group2 None
Webui | Local None
SSH | Local None
Output from the show accounting command
HP Switch(config)# show accounting Status and Counters - Accounting Information Interval(min) : 0 Suppress Empty User : No Sessions Identification : Unique Type | Method Mode Server Group -------- + ------ ---------- ------------ Network | None Exec | Radius Start-Stop group2 System | Radius Stop-Only group2 Commands | Radius Start-Stop radius