Example: Configuring user validity check
Network configuration
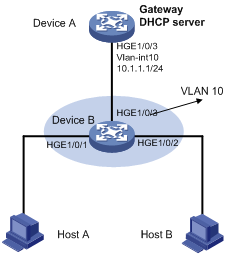
As shown in Figure 162, configure Device B to perform user validity check based on 802.1X security entries for connected hosts.
Figure 162: Network diagram
Procedure
Add all interfaces on Device B to VLAN 10, and specify the IP address of VLAN-interface 10 on Device A. (Details not shown.)
Configure the DHCP server on Device A, and configure DHCP address pool 0.
<DeviceA> system-view [DeviceA] dhcp enable [DeviceA] dhcp server ip-pool 0 [DeviceA-dhcp-pool-0] network 10.1.1.0 mask 255.255.255.0
Configure Host A and Host B as 802.1X clients and configure them to upload IP addresses for ARP attack detection. (Details not shown.)
Configure Device B:
# Enable 802.1X.
<DeviceB> system-view [DeviceB] dot1x [DeviceB] interface hundredgige 1/0/1 [DeviceB-HundredGigE1/0/1] dot1x [DeviceB-HundredGigE1/0/1] quit [DeviceB] interface hundredgige 1/0/2 [DeviceB-HundredGigE1/0/2] dot1x [DeviceB-HundredGigE1/0/2] quit
# Add a local user test.
[DeviceB] local-user test [DeviceB-luser-test] service-type lan-access [DeviceB-luser-test] password simple test [DeviceB-luser-test] quit
# Enable ARP attack detection for VLAN 10 to check user validity based on 802.1X entries.
[DeviceB] vlan 10 [DeviceB-vlan10] arp detection enable
# Configure the upstream interface as an ARP trusted interface. By default, an interface is an untrusted interface.
[DeviceB-vlan10] interface hundredgige 1/0/3 [DeviceB-HundredGigE1/0/3] arp detection trust [DeviceB-HundredGigE1/0/3] quit
Verifying the configuration
# Verify that ARP packets received on interfaces HundredGigE 1/0/1 and HundredGigE 1/0/2 are checked against 802.1X entries.