Configuring portal stateful failover
Network requirements
As shown in Figure 56, a failover link is present between Switch A and Switch B. Both Switch A and Switch B support portal authentication. Configure stateful failover between Switch A and Switch B to support portal service backup and use VRRP to implement traffic switchover between the switches. More specifically,
When Switch A works normally, Host accesses Switch A for portal authentication before accessing the Internet; when Switch A fails, Host accesses the Internet through Switch B. The VRRP uplink/downlink detection mechanism is used to ensure non-stop traffic forwarding.
Use the RADIUS server as the authentication/accounting server. In this example, Server takes the responsibilities of the portal server and the RADIUS server.
Switch A and Switch B use the failover link to transmit stateful failover related packets and specify VLAN 8 on the switches as the VLAN dedicated for stateful failover related packets.
Figure 56: Network diagram
Configuration prerequisites and guidelines
Configure IP addresses for the host, server, and switches as shown in Figure 56 and make sure they can reach to each other.
Make sure the host can access the authentication server through Switch A and Switch B.
Configure VRRP group 1 and VRRP group 2 to implement backup for downstream and upstream links respectively. For more information about VRRP, see High Availability Configuration Guide.
For information about stateful failover configuration, see High Availability Configuration Guide.
Configuring the portal server
This example assumes that the portal server runs on IMC PLAT 5.0(E0101) and IMC UAM 5.0(E0101).
# Configure the portal server.
Log in to IMC and select the Service tab. Then, select User Access Manager > Portal Service Management > Server from the navigation tree to enter the portal server configuration page, as shown in Figure 57.
Configure the portal server parameters as needed. This example uses the default settings.
Figure 57: Portal server configuration
# Configure the IP address group.
Select User Access Manager > Portal Service Management > IP Group from the navigation tree to enter the portal IP address group configuration page. Then, click Add to enter the page shown in Figure 58.
Enter the IP group name.
Enter the start IP address and end IP address of the IP group. Make sure that the host IP address is in the IP group.
Select a service group. By default, the group Ungrouped is used.
Select the IP group type Normal.
Figure 58: Adding an IP address group
# Add a portal device.
Select User Access Manager > Portal Service Management > Device from the navigation tree to enter the portal device configuration page. Then, click Add to enter the page shown in Figure 59.
Enter the device name NAS.
Enter the virtual IP address of the VRRP group that holds the portal-enabled interface.
Enter the key, which must be the same as that configured on the switches.
Set whether to enable IP address reallocation. This example uses direct portal authentication, and therefore select No from the Reallocate IP list.
Set whether to support the portal server heartbeat and user heartbeat functions. In this example, select No for both Support Server Heartbeat and Support User Heartbeat.
Figure 59: Adding a portal device

# Associate the portal device with the IP address group.
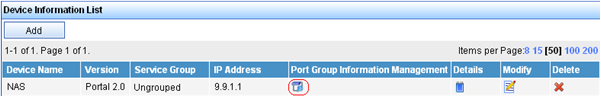
As shown in Figure 60, click the icon in the Port Group Information Management column of device NAS to enter the port group configuration page.
Figure 60: Device list
On the port group configuration page, click Add to enter the page shown in Figure 61. Perform the following configurations:
Enter the port group name.
Select the configured IP address group. The IP address used by the user to access the network must be within this IP address group.
Use the default settings for other parameters.
Figure 61: Adding a port group
# Select User Access Manager > Service Parameters > Validate System Configuration from the navigation tree to validate the configurations.
Configuring Switch A
Configure VRRP:
# Create VRRP group 1, and configure the virtual IP address of the VRRP group 1 as 9.9.1.1.
<SwitchA> system-view [SwitchA] interface vlan-interface 10 [SwitchA–Vlan-interface10] vrrp vrid 1 virtual-ip 9.9.1.1
# Set the priority of VLAN-interface 10 in VRRP group 1 to 200.
[SwitchA–Vlan-interface10] vrrp vrid 1 priority 200
# On VLAN-interface 10, configure the interface to be tracked as VLAN-interface 20 and reduce the priority of VLAN-interface 10 in VRRP group 1 by 150 when the interface state of VLAN-interface 20 becomes Down or Removed.
[SwitchA–Vlan-interface10] vrrp vrid 1 track interface vlan-interface20 reduced 150 [SwitchA–Vlan-interface10] quit
# Create VRRP group 2, and configure the virtual IP address of the VRRP group 2 as 192.168.0.1.
[SwitchA] interface vlan-interface 20 [SwitchA–Vlan-interface20] vrrp vrid 2 virtual-ip 192.168.0.1
# Set the priority of VLAN-interface 20 in VRRP group 2 to 200.
[SwitchA–Vlan-interface20] vrrp vrid 2 priority 200
# On VLAN-interface 20, configure the interface to be tracked as VLAN-interface 10 and reduce the priority of VLAN-interface 20 in VRRP group 2 by 150 when the interface state of VLAN-interface 10 becomes Down or Removed.
[SwitchA–Vlan-interface20] vrrp vrid 2 track interface vlan-interface10 reduced 150 [SwitchA–Vlan-interface20] quit
Configure a RADIUS scheme:
# Create RADIUS scheme rs1 and enter its view.
[SwitchA] radius scheme rs1
# Configure the server type for the RADIUS scheme. When using the IMC server, configure the RADIUS server type as extended.
[SwitchA-radius-rs1] server-type extended
# Specify the primary authentication server and primary accounting server, and configure the keys for communication with the servers.
[SwitchA-radius-rs1] primary authentication 192.168.0.111 [SwitchA-radius-rs1] primary accounting 192.168.0.111 [SwitchA-radius-rs1] key authentication simple expert [SwitchA-radius-rs1] key accounting simple expert
# Configure the access device to not carry the ISP domain name in the username sent to the RADIUS server. (Optional, configure the username format as needed.)
[SwitchA-radius-rs1] user-name-format without-domain [SwitchA-radius-rs1] quit
Configure an authentication domain:
# Create ISP domain dm1 and enter its view.
[SwitchA] domain dm1
# Configure AAA methods for the ISP domain.
[SwitchA-isp-dm1] authentication portal radius-scheme rs1 [SwitchA-isp-dm1] authorization portal radius-scheme rs1 [SwitchA-isp-dm1] accounting portal radius-scheme rs1 [SwitchA-isp-dm1] quit
# Configure domain dm1 as the default ISP domain for all users. Then, if a user enters a username without any ISP domain at logon, the authentication and accounting methods of the default domain are used for the user.
[SwitchA] domain default enable dm1
Enable portal authentication on the interface connecting the host:
# Configure a portal server on the switch, specifying the portal server name as newpt, IP address as 192.168.0.111, key as plaintext string portal, port number as 50100, and URL as http://192.168.0.111:8080/portal.
[SwitchA] portal server newpt ip 192.168.0.111 key simple portal port 50100 url http://192.168.0.111:8080/portal
# Enable portal authentication on the interface connecting the host.
[SwitchA] interface vlan-interface 10 [SwitchA–Vlan-interface10] portal server newpt method layer3
# Specify the source IP address of outgoing portal packets as 9.9.1.1, the virtual IP address of VRRP group 1.
[SwitchA–Vlan-interface10] portal nas-ip 9.9.1.1
Configure portal stateful failover:
# Assign interface VLAN-interface 10 to portal group 1.
[SwitchA–Vlan-interface10] portal backup-group 1 [SwitchA–Vlan-interface10] quit
# Set the device ID for Switch A in stateful failover mode to 1.
[SwitchA] nas device-id 1
# Specify the source IP address of outgoing RADIUS packets as 192.168.0.1, the virtual IP address of VRRP group 2.
[SwitchA] radius nas-ip 192.168.0.1
Make sure that you have added the access device with IP address 192.168.0.1 on the RADIUS server.
Configure the stateful failover function:
# Configure the VLAN for stateful failover as VLAN 8.
[SwitchA] dhbk vlan 8
# Enable stateful failover and configure it to support the symmetric path.
[SwitchA] dhbk enable backup-type symmetric-path
Configuring Switch B
Configure VRRP:
# Create VRRP group 1, and configure the virtual IP address of the VRRP group 1 as 9.9.1.1.
<SwitchB> system-view [SwitchB] interface vlan-interface 10 [SwitchB–Vlan-interface10] vrrp vrid 1 virtual-ip 9.9.1.1
# Set the priority of VLAN-interface 10 in VRRP group 1 to 150.
[SwitchB–Vlan-interface10] vrrp vrid 1 priority 150 [SwitchB–Vlan-interface10] quit
# Create VRRP group 2, and configure the virtual IP address of the VRRP group 2 as 192.168.0.1.
[SwitchB] interface vlan-interface 20 [SwitchB–Vlan-interface20] vrrp vrid 2 virtual-ip 192.168.0.1
# Set the priority of VLAN-interface 20 in VRRP group 2 to 150.
[SwitchB–Vlan-interface20] vrrp vrid 2 priority 150 [SwitchB–Vlan-interface20] quit
Configure a RADIUS scheme:
# Create RADIUS scheme rs1 and enter its view.
[SwitchB] radius scheme rs1
# Configure the server type for the RADIUS scheme. When using the IMC server, configure the RADIUS server type as extended.
[SwitchB-radius-rs1] server-type extended
# Specify the primary authentication server and primary accounting server, and configure the keys for communication with the servers.
[SwitchB-radius-rs1] primary authentication 192.168.0.111 [SwitchB-radius-rs1] primary accounting 192.168.0.111 [SwitchB-radius-rs1] key authentication simple expert [SwitchB-radius-rs1] key accounting simple expert
# Configure the access device to not carry the ISP domain name in the username sent to the RADIUS server. (Optional, configure the username format as needed.)
[SwitchB-radius-rs1] user-name-format without-domain [SwitchB-radius-rs1] quit
Configure an authentication domain:
# Create ISP domain dm1 and enter its view.
[SwitchB] domain dm1
# Configure AAA methods for the ISP domain.
[SwitchB-isp-dm1] authentication portal radius-scheme rs1 [SwitchB-isp-dm1] authorization portal radius-scheme rs1 [SwitchB-isp-dm1] accounting portal radius-scheme rs1 [SwitchB-isp-dm1] quit
# Configure domain dm1 as the default ISP domain for all users. Then, if a user enters a username without any ISP domain at logon, the authentication and accounting methods of the default domain are used for the user.
[SwitchB] domain default enable dm1
Enable portal authentication on the interface connecting the host:
# Configure the portal server as needed.
[SwitchB] portal server newpt ip 192.168.0.111 key simple portal port 50100 url http://192.168.0.111:8080/portal
# Enable portal authentication on the interface connecting the host.
[SwitchB] interface vlan-interface 10 [SwitchB–Vlan-interface10] portal server newpt method layer3
# Specify the source IP address of outgoing portal packets as 9.9.1.1, the virtual IP address of VRRP group 1.
[SwitchA–Vlan-interface10] portal nas-ip 9.9.1.1
Configure portal stateful failover:
# Assign interface VLAN-interface 10 to portal group 1.
[SwitchB–Vlan-interface10] portal backup-group 1 [SwitchB–Vlan-interface10] quit
# Set the ID of the device in the stateful failover mode to 2.
[SwitchB] nas device-id 2
# Specify the source IP address of outgoing RADIUS packets as 192.168.0.1, the virtual IP address of VRRP group 2.
[SwitchB] radius nas-backup-ip 192.168.0.1
Make sure you have added the access device with IP address 192.168.0.1 on the RADIUS server.
Configure stateful failure:
# Configure the VLAN for stateful failover as VLAN 8.
[SwitchB] dhbk vlan 8
# Enable stateful failover and configure it to support the symmetric path.
[SwitchB] dhbk enable backup-type symmetric-path
Verifying the configuration
After user Host logs in through Switch A, display the user authentication information by using the display portal user command on Switch A and Switch B respectively.
[SwitchA] display portal user all Index:3 State:ONLINE SubState:NONE ACL:NONE Work-mode: primary VPN instance:NONE MAC IP Vlan Interface --------------------------------------------------------------------- 000d-88f8-0eac 9.9.1.2 10 Vlan-interface10 Total 1 user(s) matched, 1 listed. [SwitchB] display portal user all Index:2 State:ONLINE SubState:NONE ACL:NONE Work-mode: secondary VPN instance:NONE MAC IP Vlan Interface --------------------------------------------------------------------- 000d-88f8-0eac 9.9.1.2 10 Vlan-interface10 Total 1 user(s) matched, 1 listed.
The output shows that both Switch A and Switch B have the user's information. The user's working mode on Switch A is primary, and that on Switch B is secondary, which indicate that the user logged in through Switch A and the user information on Switch B was synchronized from Switch A.