Overview
This chapter describes public key management for the following asymmetric key algorithms:
Revest-Shamir-Adleman Algorithm (RSA).
Digital Signature Algorithm (DSA).
Elliptic Curve Digital Signature Algorithm (ECDSA).
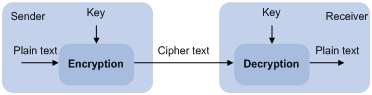
Many security applications, including SSH, SSL, and PKI, use asymmetric key algorithms to secure communications between two parties, as shown in Figure 72. Asymmetric key algorithms use two separate keys (one public and one private) for encryption and decryption. Symmetric key algorithms use only one key.
Figure 72: Encryption and decryption
A key owner can distribute the public key in plain text on the network but must keep the private key in privacy. It is mathematically infeasible to calculate the private key even if an attacker knows the algorithm and the public key.
The security applications use the asymmetric key algorithms for the following purposes:
Encryption and decryption—Any public key receiver can use the public key to encrypt information, but only the private key owner can decrypt the information.
Digital signature—The key owner uses the private key to "sign" information to be sent. The receiver decrypts the information with the sender's public key to verify information authenticity.
RSA, DSA, and ECDSA can all perform digital signature, but only RSA can perform encryption and decryption.
Asymmetric key algorithms enables secure key distribution on an insecure network, However, the security strength of an asymmetric key algorithm still depends on key size as with any symmetric key algorithm.