Configuring portal server detection and portal user synchronization
Network requirements
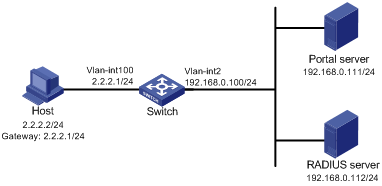
As shown in Figure 57, the host is directly connected to the switch (the access device). The host is assigned with a public IP address either manually or through DHCP. A portal server acts as both a portal authentication server and a portal Web server. A RADIUS server acts as the authentication/accounting server.
Configure direct portal authentication on the switch, so the host can access only the portal server before passing the authentication and access Internet resources after passing the authentication.
Configure the switch to do the following:
Detect the reachability state of the portal authentication server.
Send log messages upon state changes.
Disable portal authentication when the authentication server is unreachable.
Synchronize portal user information with the portal server periodically.
Figure 57: Network diagram
Configuration prerequisites and guidelines
Configure IP addresses for the switch and servers as shown in Figure 57 and make sure the host, switch, and servers can reach each other.
Configure the RADIUS server properly to provide authentication and accounting functions.
Configure the portal authentication server. Be sure to enable the server heartbeat function and the user heartbeat function.
Configure the switch (access device) as follows:
Configure direct portal authentication on VLAN-interface 100, the interface to which the host is connected.
Configure portal authentication server detection, so that the switch can detect the reachability of the portal authentication server by cooperating with the portal server heartbeat function.
Configure portal user synchronization, so that the switch can synchronize portal user information with the portal authentication server by cooperating with the portal user heartbeat function.
Configuring the portal authentication server on IMC PLAT 3.20
This example assumes that the portal server runs on IMC PLAT 3.20-R2602P13 and IMC UAM 3.60-E6301.
Configure the portal authentication server:
Log in to IMC and click the Service tab.
Select Access Service > Portal Service Management > Server from the navigation tree to enter the portal server configuration page, as shown in Figure 58.
Configure the portal server heartbeat interval and user heartbeat interval.
Use the default settings for other parameters.
Click OK.
Figure 58: Portal authentication server configuration
Configure the IP address group:
Select Access Service > Portal Service Management > IP Group from the navigation tree to enter the portal IP address group configuration page.
Click Add to enter the page shown in Figure 59.
Enter the IP group name.
Enter the start IP address and end IP address of the IP group.
Make sure the host IP address (2.2.2.2) is in the IP group.
Select a service group.
This example uses the default group Ungrouped.
Select Normal from the Action list.
Click OK.
Figure 59: Adding an IP address group
Add a portal device:
Select Access Service > Portal Service Management > Device from the navigation tree to enter the portal device configuration page.
Click Add to enter the page shown in Figure 60.
Enter the device name NAS.
Enter the IP address of the switch's interface connected to the host.
Enter the key, which must be the same as that configured on the switch.
Set whether to enable IP address reallocation.
This example uses direct portal authentication, and therefore select No from the Reallocate IP list.
Set whether to support the portal server heartbeat and user heartbeat functions.
In this example, select Yes for both Support Server Heartbeat and Support User Heartbeat.
Click OK.
Figure 60: Adding a portal device
Associate the portal device with the IP address group:
As shown in Figure 61, click the icon in the Port Group Information Management column of device NAS to enter the port group configuration page.
Figure 61: Device list

Click Add to enter the page shown in Figure 62.
Figure 62: Port group configuration

Enter the port group name.
Select the configured IP address group.
The IP address used by the user to access the network must be within this IP address group.
User default values for other parameters.
Click OK.
Select Access Service > Service Parameters > Validate System Configuration from the navigation tree to validate the configurations.
Configuring the portal authentication server on IMC PLAT 5.0
This example assumes that the portal server runs on IMC PLAT 5.0(E0101) and IMC UAM 5.0(E0101).
Configure the portal authentication server:
Log in to IMC and click the Service tab.
Select User Access Manager > Portal Service Management > Server from the navigation tree to enter the portal server configuration page, as shown in Figure 63.
Configure the portal server heartbeat interval and user heartbeat interval.
Use the default settings for other parameters.
Click OK.
Figure 63: Portal authentication server configuration
Configure the IP address group:
Select User Access Manager > Portal Service Management > IP Group from the navigation tree to enter the portal IP address group configuration page.
Click Add to enter the page shown in Figure 64.
Enter the IP group name.
Enter the start IP address and end IP address of the IP group.
Make sure the host IP address is in the IP group.
Select a service group.
This example uses the default group Ungrouped.
Select Normal from the Action list.
Click OK.
Figure 64: Adding an IP address group
Add a portal device:
Select User Access Manager > Portal Service Management > Device from the navigation tree to enter the portal device configuration page.
Click Add to enter the page shown in Figure 65.
Enter the device name NAS.
Enter the IP address of the switch's interface connected to the host.
Enter the key, which must be the same as that configured on the switch.
Set whether to enable IP address reallocation.
This example uses direct portal authentication, and therefore select No from the Reallocate IP list.
Select whether to support sever heartbeat and user heartbeat functions.
In this example, select Yes for both Support Server Heartbeat and Support User Heartbeat.
Click OK.
Figure 65: Adding a portal device
Associate the portal device with the IP address group:
As shown in Figure 66, click the icon in the Port Group Information Management column of device NAS to enter the port group configuration page.
Click Add to enter the page shown in Figure 67.
Enter the port group name.
Select the configured IP address group.
The IP address used by the user to access the network must be within this IP address group.
Use the default settings for other parameters.
Click OK.
Figure 66: Device list
Figure 67: Adding a port group
Select User Access Manager > Service Parameters > Validate System Configuration from the navigation tree to validate the configurations.
Configuring the switch
Configure a RADIUS scheme:
# Create a RADIUS scheme named rs1 and enter its view.
<Switch> system-view [Switch] radius scheme rs1
# Specify the primary authentication server and primary accounting server, and configure the keys for communication with the servers.
[Switch-radius-rs1] primary authentication 192.168.0.112 [Switch-radius-rs1] primary accounting 192.168.0.112 [Switch-radius-rs1] key authentication simple radius [Switch-radius-rs1] key accounting simple radius
# Exclude the ISP domain name from the username sent to the RADIUS server.
[Switch-radius-rs1] user-name-format without-domain [Switch-radius-rs1] quit
# Enable RADIUS session control.
[Switch] radius session-control enable
Configure an authentication domain:
# Create an ISP domain named dm1 and enter its view.
[Switch] domain dm1
# Configure AAA methods for the ISP domain.
[Switch-isp-dm1] authentication portal radius-scheme rs1 [Switch-isp-dm1] authorization portal radius-scheme rs1 [Switch-isp-dm1] accounting portal radius-scheme rs1 [Switch-isp-dm1] quit
# Configure domain dm1 as the default ISP domain. If a user enters the username without the ISP domain name at login, the authentication and accounting methods of the default domain are used for the user.
[Switch] domain default enable dm1
Configure portal authentication:
# Configure a portal authentication server.
[Switch] portal server newpt [Switch-portal-server-newpt] ip 192.168.0.111 key simple portal [Switch-portal-server-newpt] port 50100
# Configure reachability detection of the portal authentication server: set the server detection interval to 40 seconds, and send log messages upon reachability status changes.
[Switch-portal-server-newpt] server-detect timeout 40 log
![[NOTE: ]](images/note.png)
NOTE:
The value of timeout must be greater than or equal to the portal server heartbeat interval.
# Configure portal user synchronization with the portal authentication server, and set the synchronization detection interval to 600 seconds.
[Switch-portal-server-newpt] user-sync timeout 600 [Switch-portal-server-newpt] quit
![[NOTE: ]](images/note.png)
NOTE:
The value of timeout must be greater than or equal to the portal user heartbeat interval.
# Configure a portal Web server.
[Switch] portal web-server newpt [Switch-portal-websvr-newpt] url http://192.168.0.111:8080/portal [Switch-portal-websvr-newpt] quit
# Enable direct portal authentication on VLAN-interface 100.
[Switch] interface vlan-interface 100 [Switch–Vlan-interface100] portal enable method direct
# Enable portal fail-permit for the portal authentication server newpt.
[Switch–Vlan-interface100] portal fail-permit server newpt
# Reference the portal Web server newpt on VLAN-interface 100.
[Switch–Vlan-interface100] portal apply web-server newpt
# Configure the BAS-IP as 2.2.2.1 for portal packets sent from VLAN-interface 100 to the portal authentication server.
[Switch–Vlan-interface100] portal bas-ip 2.2.2.1 [Switch–Vlan-interface100] quit
Verifying the configuration
# Use the following command to display information about the portal authentication server.
[Switch] display portal server newpt Portal server: newpt IP : 192.168.0.111 VPN instance : -- Port : 50100 Server Detection : Timeout 40s Action: log User synchronization : Timeout 600s Status : Up
The Up status of the portal authentication server indicates that the portal authentication server is reachable. If the access device detects that the portal authentication server is unreachable, the Status field in the command output displays Down. The access device generates a server unreachable log "Portal server newpt turns down from up" and disables portal authentication on the access interface, so the host can access the external network without authentication.