Outbound one-to-one static NAT configuration example
Network requirements
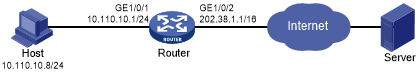
Configure static NAT to allow the host at 10.110.10.8/24 to access the Internet.
Figure 56: Network diagram
Configuration procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Configure a one-to-one static NAT mapping between the private address 10.110.10.8 and the public address 202.38.1.100.
<Router> system-view [Router] nat static outbound 10.110.10.8 202.38.1.100
# Enable static NAT on GigabitEthernet 1/0/2.
[Router] interface gigabitethernet 1/0/2 [Router-GigabitEthernet1/0/2] nat static enable
Verifying the configuration
# Verify that the host at 10.110.10.8/24 can access the server on the Internet. (Details not shown.)
# Display static NAT configuration.
[Router] display nat static
Static NAT mappings:
Totally 1 outbound static NAT mappings.
IP-to-IP:
Local IP : 10.110.10.8
Global IP : 202.38.1.100
Config status: Active
Interfaces enabled with static NAT:
Totally 1 interfaces enabled with static NAT.
Interface: GigabitEthernet1/0/2
Config status: Active
# Display NAT session information.
[Router] display nat session verbose Initiator: Source IP/port: 10.110.10.8/42496 Destination IP/port: 202.38.1.111/2048 DS-Lite tunnel peer: - VPN instance/VLAN ID/Inline ID: -/-/- Protocol: ICMP(1) Inbound interface: GigabitEthernet1/0/1 Responder: Source IP/port: 202.38.1.111/42496 Destination IP/port: 202.38.1.100/0 DS-Lite tunnel peer: - VPN instance/VLAN ID/Inline ID: -/-/- Protocol: ICMP(1) Inbound interface: GigabitEthernet1/0/2 State: ICMP_REPLY Application: INVALID Start time: 2012-08-16 09:30:49 TTL: 27s Initiator->Responder: 5 packets 420 bytes Responder->Initiator: 5 packets 420 bytes Total sessions found: 1