NAT with DNS mapping configuration example
Network requirements
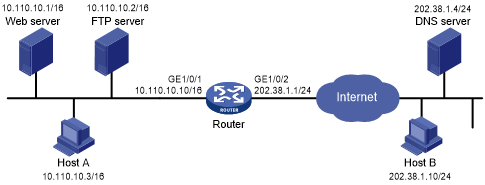
As shown in Figure 66, the internal Web server at 10.110.10.1/16 and FTP server at 10.110.10.2/16 provide services for external user. The company has three public addresses 202.38.1.1 through 202.38.1.3. The DNS server at 202.38.1.4 is on the external network.
Configure NAT so that:
The public IP address 202.38.1.2 is used by external users to access the Web and FTP servers.
External users can use the public address or domain name of internal servers to access them.
Internal users can access the internal servers by using their domain names.
Figure 66: Network diagram
Requirements analysis
To meet the network requirements, perform the following tasks:
Configure NAT Server by mapping the public IP addresses and port numbers of the internal servers to a public address and port numbers so that external users can access the internal servers.
Configure NAT with DNS mapping and ALG so that the public IP address of the internal server in the payload of the DNS response packet can be translated to the private IP address.
Configuration procedure
# Specify IP addresses for the interfaces on the router. (Details not shown.)
# Enable NAT with ALG for DNS.
<Router> system-view [Router] nat alg dns
# Enter interface view of GigabitEthernet 1/0/2.
[Router] interface gigabitethernet 1/0/2
# Configure NAT Server to allow external hosts to access the internal Web server by using the address 202.38.1.2.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.2 inside 10.110.10.1 http
# Configure NAT Server to allow external hosts to access the internal FTP server by using the address 202.38.1.2.
[Router-GigabitEthernet1/0/2] nat server protocol tcp global 202.38.1.2 inside 10.110.10.2 ftp
# Enable outbound NAT with Easy IP on interface GigabitEthernet 1/0/2.
[Router-GigabitEthernet1/0/2] nat outbound
# Configure two DNS mapping entries by mapping the domain name www.server.com of the Web server to 202.38.1.2, and ftp.server.com of the FTP server to 202.38.1.2.
[Router] nat dns-map domain www.server.com protocol tcp ip 202.38.1.2 port http [Router] nat dns-map domain ftp.server.com protocol tcp ip 202.38.1.2 port ftp [Router] quit
Verifying the configuration
# Verify that both internal and external hosts can access the internal servers by using domain names. (Details not shown.)
# Display all NAT configuration and statistics.
[Router] display nat all
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: GigabitEthernet1/0/2
ACL: ---
Address group ID: ---
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT internal server information:
Totally 2 internal servers.
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.2/21
Local IP/port : 10.110.10.2/21
Config status : Active
Interface: GigabitEthernet1/0/2
Protocol: 6(TCP)
Global IP/port: 202.38.1.2/80
Local IP/port : 10.110.10.1/80
Config status : Active
NAT DNS mapping information:
Totally 2 NAT DNS mappings.
Domain name: ftp.server.com
Global IP : 202.38.1.2
Global port: 21
Protocol : TCP(6)
Config status: Active
Domain name: www.server.com
Global IP : 202.38.1.2
Global port: 80
Protocol : TCP(6)
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NAT mapping behavior:
Mapping mode: Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RSH : Enabled
RTSP : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled