Configuring trusted ports
In a similar way to DHCP snooping, dynamic ARP protection allows you to configure VLAN interfaces in two categories: trusted and untrusted ports. ARP packets received on trusted ports are forwarded without validation.
The switch intercepts all ARP requests and responses on the port.
Each intercepted packet is checked to see if its IP-to-MAC binding is valid. If a binding is invalid, the switch drops the packet.
In contrast, if Switch A does not support dynamic ARP protection and you configure the port on Switch B connected to Switch A as trusted, Switch B opens itself to possible ARP poisoning from hosts attached to Switch A.
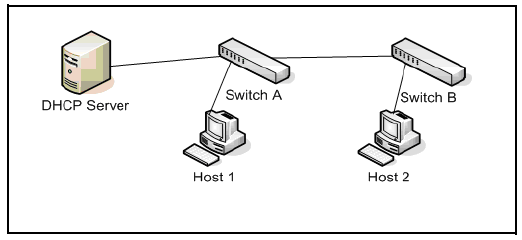
Configure ports connected to other switches in the network as trusted ports. In this way, all network switches can exchange ARP packets and update their ARP caches with valid information.
Switches that do not support dynamic ARP protection must be separated by a router in their own Layer 2 domain. Because ARP packets do not cross Layer 3 domains, the unprotected switches cannot unknowingly accept ARP packets from an attacker and forward them to protected switches through trusted ports.
To configure one or more Ethernet interfaces that handle VLAN traffic as trusted ports, enter the
arp-protect trust command at the global configuration level. The switch does not check ARP requests and responses received on a trusted port.
Syntax:
[no] arp-protect trust <port-list>
port-list: Specifies a port number or a range of port numbers. Separate individual port numbers or ranges of port numbers with a comma; for example: 13-15, 17.
An example of the
arp-protect trust command is shown here:
switch(config)# arp-protect trust 5-8, 17