Configuring the switch to access a RADIUS server
This section describes how to configure the switch to interact with a RADIUS server for both authentication and accounting services.
If you want to configure RADIUS accounting on the switch, see Accounting services.
Syntax
[no] radius-server host <ip-address> [oobm]]
Adds a server to the RADIUS configuration or (with no) deletes a server from the configuration. You can configure up to three RADIUS servers, and up to 15 RADIUS server addresses. See Using multiple RADIUS server groups for information about grouping multiple RADIUS servers.
The switch uses the first server it successfully accesses, see Changing RADIUS-server access order.
For switches that have a separate out-of-band management port, the
oobm parameter specifies that the RADIUS traffic goes through the out-of-band management (OOBM) port.
[auth-port | <port-number>]
Optional. Changes the UDP destination port for authentication requests to the specified RADIUS server (host). If you do not use this option with the
radius-server host command, the switch automatically assigns the default authentication port number. The
auth-port number must match its server counterpart.
Default: 1812
[acct-port | <port-number>]
Optional. Changes the UDP destination port for accounting requests to the specified RADIUS server. If you do not use this option with the RADIUS-server host command, the switch automatically assigns the default accounting port number. The
acct-port number must match its server counterpart.
Default: 1813
[dyn-authorization]
Enables or disables the processing of Disconnect and Change of Authorization messages from this host. When enabled, the RADIUS server can dynamically terminate or change the authorization parameters (such as VLAN assignment) used in an active client session on the switch. The UDP port specified in the
radius-server dyn-autz-port command (defaults to 3799) is the port used to listen for Change of Authorization messages (CoA) or Disconnect messages (DM). See
Additional RADIUS attributes.
Default: Disabled
[key <key-string>
Optional. Specifies an encryption key for use during authentication (or accounting) sessions with the specified server. This key must match the encryption key used on the RADIUS server. Use this command only if the specified server requires a different encryption key than configured for the global encryption key.
Formerly, when you saved the configuration file using Xmodem or TFTP, the RADIUS encryption key information was not saved in the file. This caused RADIUS authentication to break when the startup configuration file was loaded back onto the switch. You now can save the configured RADIUS shared secret (encryption) key to a configuration file by entering the commands listed.
include-credentialswrite memoryFor more information, see
[encrypted-key <key-string>]
Encryption key to use with the RADIUS server, specified using a base64–encoded aes-256 encrypted string.
[time-window <0-65535>]The time window in seconds within which the received dynamic authorization requests are considered to be current and accepted for processing. A zero value means there is no time limit. A non-zero value indicates that the even-timestamp attribute is expected as part of all Change of Authorization and Disconnect request messages. If the timestamp attribute is not present the message is dropped.
Default: 300 seconds.
no radius-server host <ip-address> key
Use the
no form of the command to remove the key for a specified server.
Example
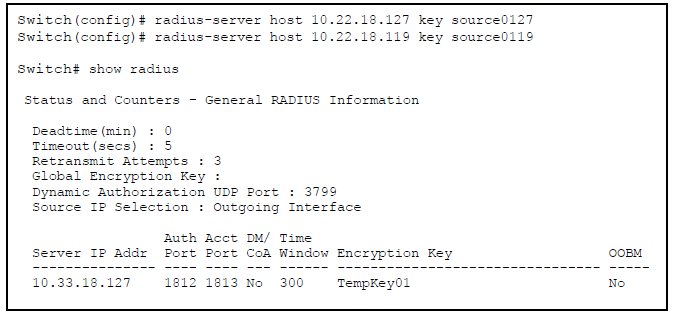
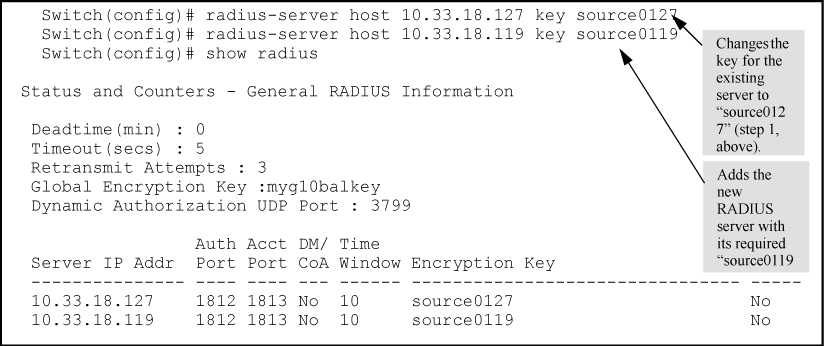
Suppose you have configured the switch as shown in Sample configuration for RADIUS server before changing the key and adding another server and you now need to make the following changes:
- Change the encryption key for the server at 10.33.18.127 to "source0127".
- Add a RADIUS server with an IP address of 10.33.18.119 and a server-specific encryption key of "source0119".
To make these changes, perform the following:
To change the order in which the switch accesses RADIUS servers, see Changing RADIUS-server access order.